If you are looking for PKI and Applications you've visit to the right web. We have 15 Pictures about PKI and Applications like How PKI Works ? - RebelAdmin.com, Pki Diagram and also Overview of Public Key Infrastructure, Certificate Management and. Here it is:
PKI And Applications
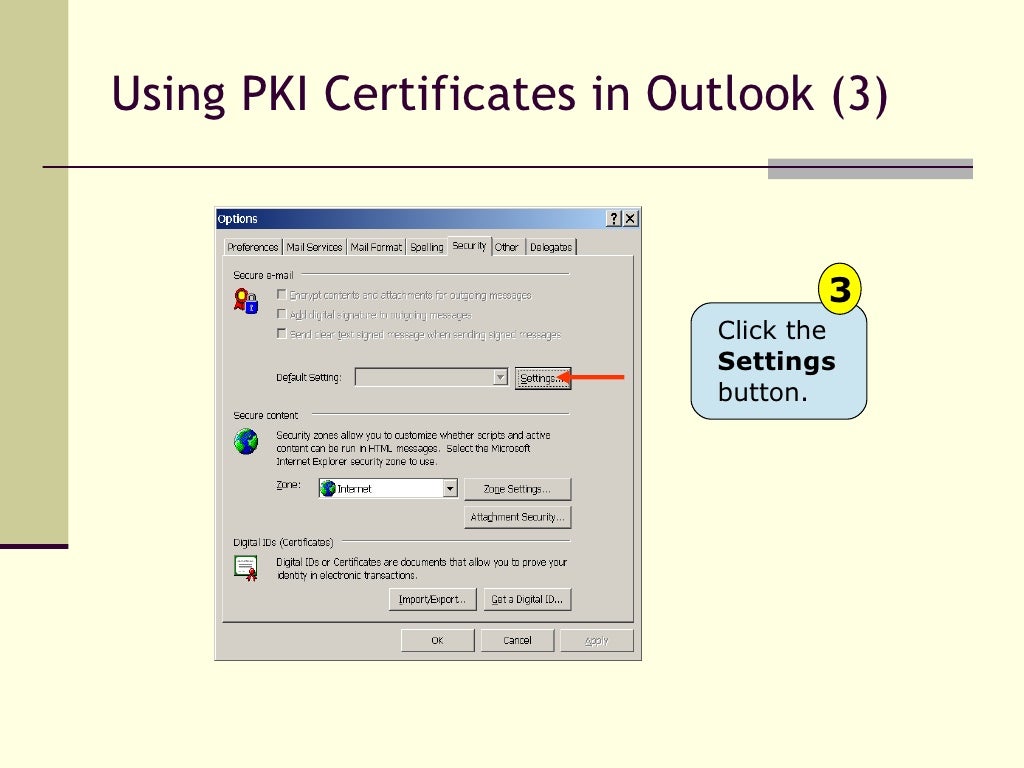 www.slideshare.net
www.slideshare.net pki
Review – “The Seven Properties Of Highly Secure Devices” From Microsoft
 iotgossiper.com
iotgossiper.com pki certificate highly secure properties process deployment models devices microsoft seven rebeladmin hierarchy directory active standalone certificates cas created
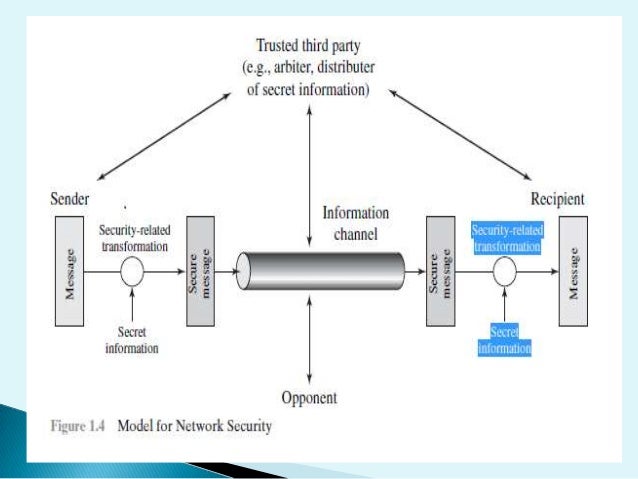
The Internet Overview An Introduction To
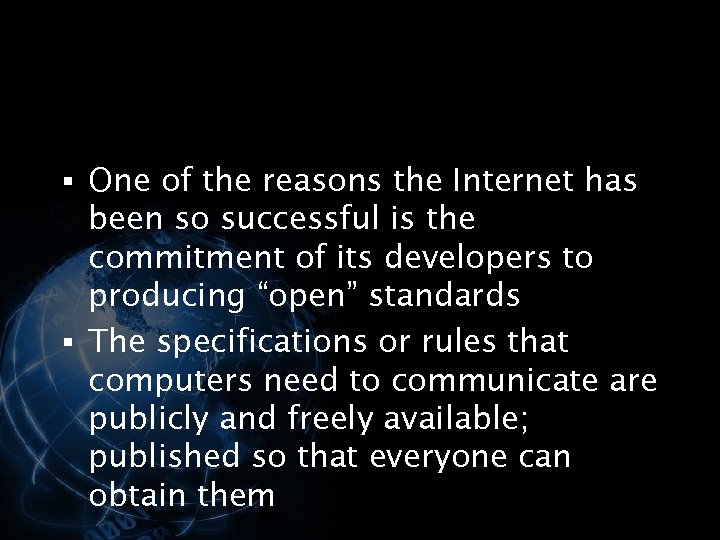 present5.com
present5.com internet introduction overview ppt
Pki Diagram
 bishosoft.com
bishosoft.com pki diagram
The Internet Overview An Introduction To
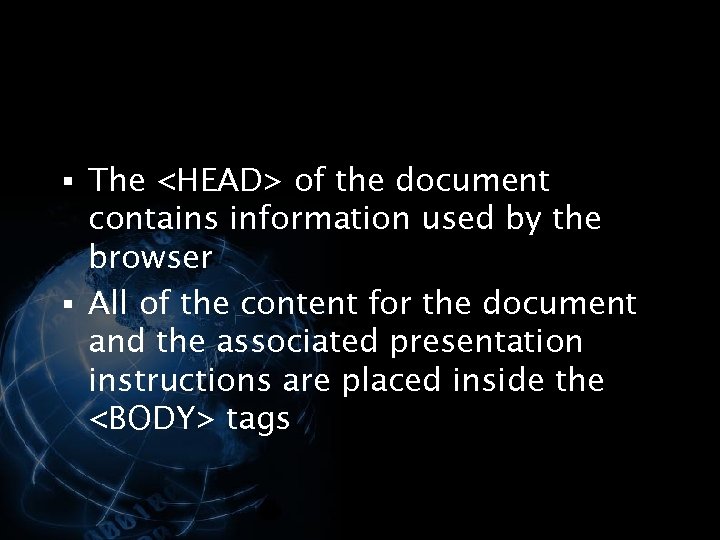 present5.com
present5.com internet introduction overview advertisements
The Internet Overview An Introduction To
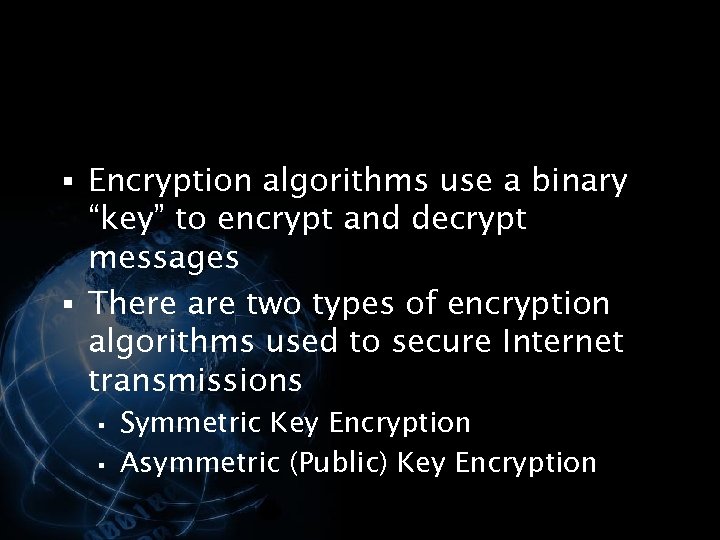 present5.com
present5.com introduction overview internet advertisements
The Internet Overview An Introduction To
 present5.com
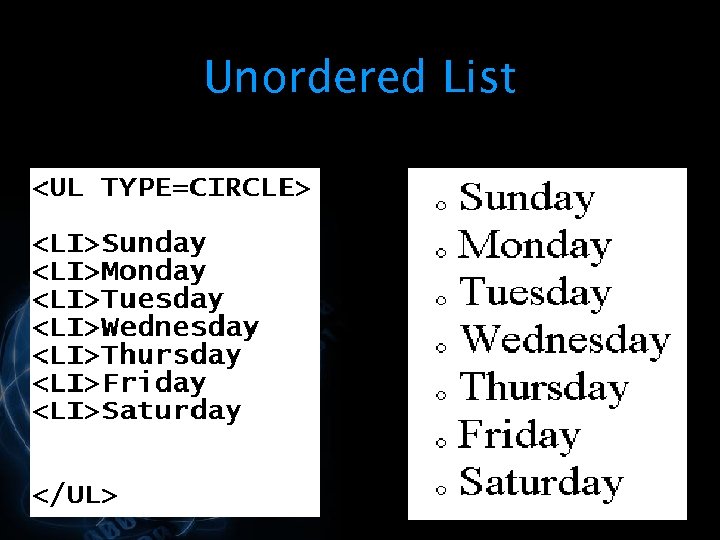
present5.com internet introduction overview list unordered advertisements
Overview Of Public Key Infrastructure, Certificate Management And
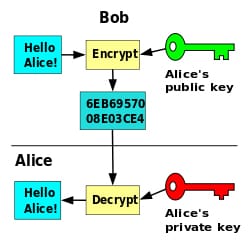 www.examcollection.com
www.examcollection.com key infrastructure components overview cryptography encryption keys associated certificate management wikipedia examcollection
Summary Of Protocols For PKI Interoperability
 www.entrust.com
www.entrust.com pki summary interoperability protocols component brief purpose each entrust
Fundamentals Of PKI Authentication - Gemalto Blog
 blog.gemalto.com
blog.gemalto.com pki authentication fundamentals gemalto
Public Key Infrastructure: Digital Certificates (HTTPS, SSL)
key digital infrastructure certificates certificate process communication exchange web certification basics server webmail defined checking activedirectoryfaq runs according channel company
Basic Concept Of Pki
 www.slideshare.net
www.slideshare.net pki
Understanding Cisco Routing Tables With Route Print Find My IP
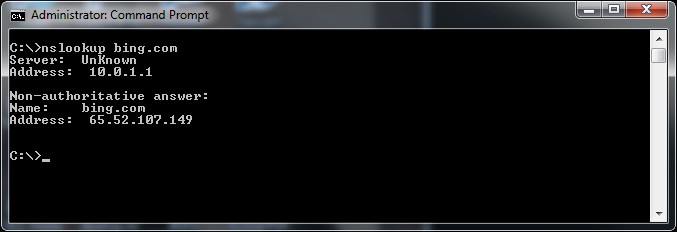 www.interfacett.com
www.interfacett.com cisco nslookup routing
The Internet Overview An Introduction To
 present5.com
present5.com introduction overview internet advertisements data
How PKI Works ? - RebelAdmin.com
pki works process rebeladmin
Summary of protocols for pki interoperability. The internet overview an introduction to. Pki diagram
if you are looking "id":107,"keyword_id":2,"name":"PKI Example","scraped_at":"2022-10-01 03:08:02","created_at":"2022-10-01T03:08:02.000000Z","updated_at":"2022-10-01T03:08:02.000000Z","images":["id":1696,"keyword_id":107,"url":"http:\/\/www.rebeladmin.com\/wp-content\/uploads\/2018\/05\/pki6.png","link":"http:\/\/www.rebeladmin.com\/2018\/05\/how-pki-works\/","title":"How PKI Works ? - RebelAdmin.com","thumbnail":"https:\/\/tse4.mm.bing.net\/th?id=OIP.O0rojEYpa8moff6jtAx-EgHaDc&pid=15.1","size":"924 x 429 \u00b7 png","desc":"pki works process rebeladmin","filetype":"png","width":924,"height":429,"domain":"www.rebeladmin.com","created_at":null,"updated_at":null,"id":1697,"keyword_id":107,"url":"http:\/\/bp0.blogger.com\/_2xduua7nmyw\/SIUoRSXs5bI\/AAAAAAAAAQg\/C49rqGDuoro\/s400\/Figure%2B2%2B-%2BStandard%2BPKI%2BInfrastructure.jpg","link":"http:\/\/bishosoft.com\/js\/pki-diagram","title":"Pki Diagram","thumbnail":"https:\/\/tse3.mm.bing.net\/th?id=OIP.h_qT7QNndLn-lRfoigqCnwAAAA&pid=15.1","size":"400 x 325 \u00b7 jpeg","desc":"pki diagram","filetype":"jpg","width":400,"height":325,"domain":"bishosoft.com","created_at":null,"updated_at":null,"id":1698,"keyword_id":107,"url":"https:\/\/www.entrust.com\/-\/media\/entrust\/resources\/product-support\/certificate-solutions\/managedpki.gif?la=en&hash=2162166F1AE7DDF23B5BF6CDFDAB7B6C","link":"https:\/\/www.entrust.com\/resources\/certificate-solutions\/learn\/summary-of-protocols-for-pki-interoperability","title":"Summary of Protocols for PKI Interoperability","thumbnail":"https:\/\/tse2.mm.bing.net\/th?id=OIP.ny2hOu37ohdTioUq2S18bQAAAA&pid=15.1","size":"418 x 246 \u00b7 gif","desc":"pki summary interoperability protocols component brief purpose each entrust","filetype":"gif","width":418,"height":246,"domain":"www.entrust.com","created_at":null,"updated_at":null,"id":1699,"keyword_id":107,"url":"https:\/\/image.slidesharecdn.com\/pkiandapplications-1213824493775384-9\/95\/pki-and-applications-38-1024.jpg?cb=1213799136","link":"https:\/\/www.slideshare.net\/nakov\/pki-and-applications","title":"PKI and Applications","thumbnail":"https:\/\/tse3.mm.bing.net\/th?id=OIP.zGJCoH7TwAJ2_3GBM9sj_QHaFj&pid=15.1","size":"1024 x 768 \u00b7 jpeg","desc":"pki","filetype":"jpg","width":1024,"height":768,"domain":"www.slideshare.net","created_at":null,"updated_at":null,"id":1700,"keyword_id":107,"url":"https:\/\/blog.gemalto.com\/wp-content\/uploads\/2017\/01\/pki-fundamentals.png","link":"https:\/\/blog.gemalto.com\/security\/2017\/01\/10\/fundamentals-pki-authentication\/","title":"Fundamentals of PKI Authentication - Gemalto blog","thumbnail":"https:\/\/tse1.mm.bing.net\/th?id=OIP.D_9R68taDKt8uOdGDUr3LwAAAA&pid=15.1","size":"246 x 217 \u00b7 png","desc":"pki authentication fundamentals gemalto","filetype":"png","width":246,"height":217,"domain":"blog.gemalto.com","created_at":null,"updated_at":null,"id":1701,"keyword_id":107,"url":"https:\/\/image.slidesharecdn.com\/basicconceptofpki-130426145529-phpapp01\/95\/basic-concept-of-pki-6-638.jpg?cb=1366988166","link":"https:\/\/www.slideshare.net\/PrabhatGoel1\/basic-concept-of-pki","title":"Basic concept of pki","thumbnail":"https:\/\/tse1.mm.bing.net\/th?id=OIP.DG5t_Eyz8X4u4mO7HKLZoQHaFj&pid=15.1","size":"638 x 479 \u00b7 jpeg","desc":"pki","filetype":"jpg","width":638,"height":479,"domain":"www.slideshare.net","created_at":null,"updated_at":null,"id":1702,"keyword_id":107,"url":"https:\/\/i1.wp.com\/www.rebeladmin.com\/wp-content\/uploads\/2018\/05\/ca3.png","link":"https:\/\/iotgossiper.com\/2019\/09\/11\/review-the-seven-properties-of-highly-secure-devices-from-microsoft\/","title":"Review \u2013 \u201cThe Seven Properties of Highly Secure Devices\u201d from Microsoft","thumbnail":"https:\/\/tse2.mm.bing.net\/th?id=OIP.Q0wQp2L-_-OoNaDcZDlj7gHaF2&pid=15.1","size":"604 x 477 \u00b7 png","desc":"pki certificate highly secure properties process deployment models devices microsoft seven rebeladmin hierarchy directory active standalone certificates cas created","filetype":"png","width":604,"height":477,"domain":"iotgossiper.com","created_at":null,"updated_at":null,"id":1703,"keyword_id":107,"url":"https:\/\/www.examcollection.com\/design\/wikipic\/256.jpg","link":"https:\/\/www.examcollection.com\/certification-training\/security-plus-overview-of-public-key-infrastructure-certificate-management-and-associated-components.html","title":"Overview of Public Key Infrastructure, Certificate Management and","thumbnail":"https:\/\/tse4.mm.bing.net\/th?id=OIP.X0OSENHXrPxW9UOeVbOjawAAAA&pid=15.1","size":"250 x 244 \u00b7 jpeg","desc":"key infrastructure components overview cryptography encryption keys associated certificate management wikipedia examcollection","filetype":"jpg","width":250,"height":244,"domain":"www.examcollection.com","created_at":null,"updated_at":null,"id":1704,"keyword_id":107,"url":"http:\/\/activedirectoryfaq.com\/wp-content\/uploads\/2014\/08\/public-key-infrastructure-digital-certificates-1024x480.png","link":"http:\/\/activedirectoryfaq.com\/2014\/08\/public-key-infrastructure-basics-about-digital-certificates-https-ssl\/","title":"Public Key Infrastructure: Digital certificates (HTTPS, SSL)","thumbnail":"https:\/\/tse2.mm.bing.net\/th?id=OIP.idjUtKyGmSN8ggSaNgrqrAHaDe&pid=15.1","size":"1024 x 480 \u00b7 png","desc":"key digital infrastructure certificates certificate process communication exchange web certification basics server webmail defined checking activedirectoryfaq runs according channel company","filetype":"png","width":1024,"height":480,"domain":"activedirectoryfaq.com","created_at":null,"updated_at":null,"id":1705,"keyword_id":107,"url":"https:\/\/www.interfacett.com\/wp-content\/uploads\/2012\/04\/003-nslookup-IP-address-windows-command-prompt-Cisco-routing-tables-with-route-print.png","link":"http:\/\/www.interfacett.com\/blogs\/understanding-cisco-routing-tables-with-route-print\/","title":"Understanding Cisco routing tables with route print find my IP","thumbnail":"https:\/\/tse3.mm.bing.net\/th?id=OIP.nRj0CkmPG1TLLKgMBNHG7AHaCi&pid=15.1","size":"677 x 232 \u00b7 jpeg","desc":"cisco nslookup routing","filetype":"jpg","width":677,"height":232,"domain":"www.interfacett.com","created_at":null,"updated_at":null,"id":1706,"keyword_id":107,"url":"https:\/\/present5.com\/presentation\/534fb19deda8d661a65743880572bcb7\/image-30.jpg","link":"https:\/\/present5.com\/the-internet-overview-an-introduction-to\/","title":"The Internet Overview An introduction to","thumbnail":"https:\/\/tse1.mm.bing.net\/th?id=OIP.FvOSEvgLCgMGSp5eeZup_AHaFj&pid=15.1","size":"720 x 540 \u00b7 jpeg","desc":"introduction overview internet advertisements data","filetype":"jpg","width":720,"height":540,"domain":"present5.com","created_at":null,"updated_at":null,"id":1707,"keyword_id":107,"url":"https:\/\/present5.com\/presentation\/534fb19deda8d661a65743880572bcb7\/image-101.jpg","link":"https:\/\/present5.com\/the-internet-overview-an-introduction-to\/","title":"The Internet Overview An introduction to","thumbnail":"https:\/\/tse4.mm.bing.net\/th?id=OIP.9j60QrVfuEF3cwk3FuURZAHaFj&pid=15.1","size":"720 x 540 \u00b7 jpeg","desc":"internet introduction overview ppt","filetype":"jpg","width":720,"height":540,"domain":"present5.com","created_at":null,"updated_at":null,"id":1708,"keyword_id":107,"url":"https:\/\/present5.com\/presentation\/534fb19deda8d661a65743880572bcb7\/image-70.jpg","link":"https:\/\/present5.com\/the-internet-overview-an-introduction-to\/","title":"The Internet Overview An introduction to","thumbnail":"https:\/\/tse3.mm.bing.net\/th?id=OIP.0UA1Q8K6dIV3bjnTqdEDmwHaFj&pid=15.1","size":"720 x 540 \u00b7 jpeg","desc":"introduction overview internet advertisements","filetype":"jpg","width":720,"height":540,"domain":"present5.com","created_at":null,"updated_at":null,"id":1709,"keyword_id":107,"url":"https:\/\/present5.com\/presentation\/534fb19deda8d661a65743880572bcb7\/image-39.jpg","link":"https:\/\/present5.com\/the-internet-overview-an-introduction-to\/","title":"The Internet Overview An introduction to","thumbnail":"https:\/\/tse2.mm.bing.net\/th?id=OIP.Wq_iGncDxdFop5iymS6mDQHaFj&pid=15.1","size":"720 x 540 \u00b7 jpeg","desc":"internet introduction overview list unordered advertisements","filetype":"jpg","width":720,"height":540,"domain":"present5.com","created_at":null,"updated_at":null,"id":1710,"keyword_id":107,"url":"https:\/\/present5.com\/presentation\/534fb19deda8d661a65743880572bcb7\/image-20.jpg","link":"https:\/\/present5.com\/the-internet-overview-an-introduction-to\/","title":"The Internet Overview An introduction to","thumbnail":"https:\/\/tse4.mm.bing.net\/th?id=OIP.WGNtjciR86u2na0N9HSJbQHaFj&pid=15.1","size":"720 x 540 \u00b7 jpeg","desc":"internet introduction overview advertisements","filetype":"jpg","width":720,"height":540,"domain":"present5.com","created_at":null,"updated_at":null] this site you are coming to the right page. Contains many images about PKI Example Introduction overview internet advertisements data. Don't forget to bookmark this page for future reference or share to facebook / twitter if you like this page.
Comments
Post a Comment